TrustZone aimed at establishing trust in ARM-based platforms. In contrast to TPMs, which were designed as fixed-function devices with a predefined feature set, TrustZone represented a much more flexible approach by leveraging the CPU as a freely programmable trusted platform module.
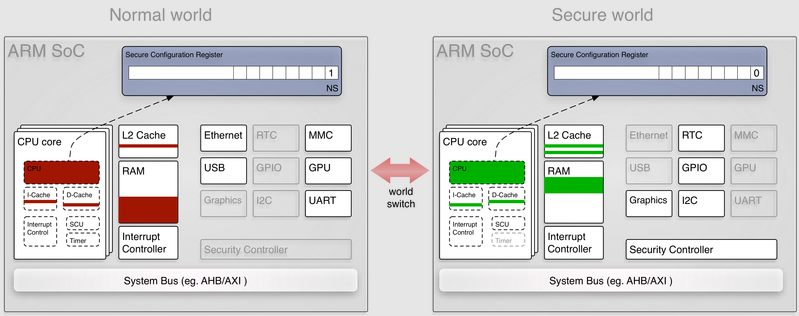
To do that, ARM introduced a special CPU mode called “secure mode” in addition to the regular normal mode, thereby establishing the notions of a “secure world” and a “normal world”. The distinction between both worlds is completely orthogonal to the normal ring protection between user-level and kernel-level code and hidden from the operating system running in the normal world. Furthermore, it is not limited to the CPU but propagated over the system bus to peripheral devices and memory controllers.
When secure mode is active, the software running on the CPU has a different view on the whole system than software running in non-secure mode. This way, system functions, in particular security functions and cryptographic credentials, can be hidden from the normal world. It goes without saying that this concept is vastly more flexible than TPM chips because the functionality of the secure world is defined by system software instead of being hard-wired.
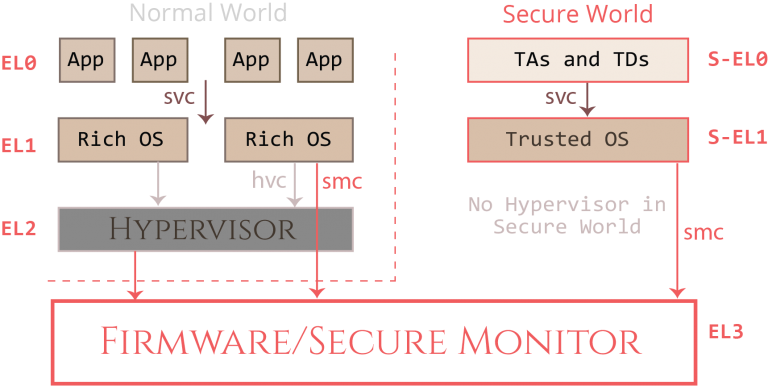
TrustZone also expands the standard “Exception Level” privilege model for the CPU. Before TrustZone, three levels existed: EL0 (user-mode), EL1 (kernel-mode) and EL2 (hypervisor-mode). TrustZone adds a new EL3 (secure monitor mode), which is the most privileged level and controls the entire system. But TrustZone also allows the CPU to run in the secure mode at lower privileges, allowing privilege isolation within the TEE itself. The CPU can therefore also run in S-EL0 (secure user-mode) and S-EL1 (secure kernel-mode).
-
**S-EL3 **operates the code for the Secure Monitor, which is the highest privilege level for the CPU. The Secure Monitor runs code from the Arm Trusted Firmware (ATF) provided by the device manufacturer. This code performs context switching between the Rich Execution Environment (REE) and TEE kernels, and provides basic services to both via the secure monitor call (SMC) handler which can be requested by REE and TEE OSes via the SMC instruction.
-
No EL2 equivalent exists in Secure World (SWd), and consequently it is not possible to run multiple virtual TEE OSes within a hypervisor inside the SWd. Support for S-EL2 has been proposed for inclusion in the Armv8.4-A profile.
-
**S-EL1 **runs the code for the Trusted Execution Environment’s operating system. Depending on the TEE implementation, Trusted Drivers may also run as S-EL1.
-
**S-EL0 **runs unprivileged “Trusted Applications” (TAs) and in certain Trusted Execution Environments (TEE) implementations even Trusted Drivers (TDs) within the TEE. By default, TAs cannot operate in the context of other TAs, directly communicate with device peripherals or interact with other processes in the Normal World (NWd) or Secure World (SWd), except as explicitly allowed by the TEE OS.
In the TrustZone architecture, each logical processor core operates as if it had two different “virtual cores”; one operating inside TrustZone and the other running outside of it. The “Normal World” (NWd) core runs the traditional operating system as before, complete with its rich functionality and normal applications. In TrustZone terminology, this entire environment is referred to as the Rich Execution Environment (REE). By contrast, the TrustZone virtual core hosts and runs a Trusted Execution Environment (TEE) in the “Secure World” (SWd). In practice, TrustZone virtual cores are implemented by fast context switching performed inside the Secure Monitor.
The normal world is active (non-secure bit is set), the OS running on the platform can only access a subset of the physical resources. When a world switch takes place, the secure world comes into effect. The system software running in the secure world can access the devices hidden from the normal world.
https://embeddedsecurity.io/sec-tz-basics.html
https://blog.quarkslab.com/introduction-to-trusted-execution-environment-arms-trustzone.html
https://azeria-labs.com/trusted-execution-environments-tee-and-trustzone/
https://www.keil.com/pack/doc/CMSIS/Core/html/using_TrustZone_pg.html
https://www.youtube.com/watch?v=7HIzQfH8tcg
https://www.youtube.com/watch?v=eOnQcWMWBsM&feature=emb_title
https://www.youtube.com/watch?v=eSOEgRoqCCI