Binary files tend to have frequent repetitions of certain instructions (e.g. prologues, nop sequences, etc) and data structures are hardly random. Long sequences of zeroes are also quite common in the data segment, when not everything can be deferred to bss. On the contrary, an encrypted file will have nearly perfect entropy, since that’s kind of the goal of a robust encryption scheme 😉
To make this check, one can use the Binwalk
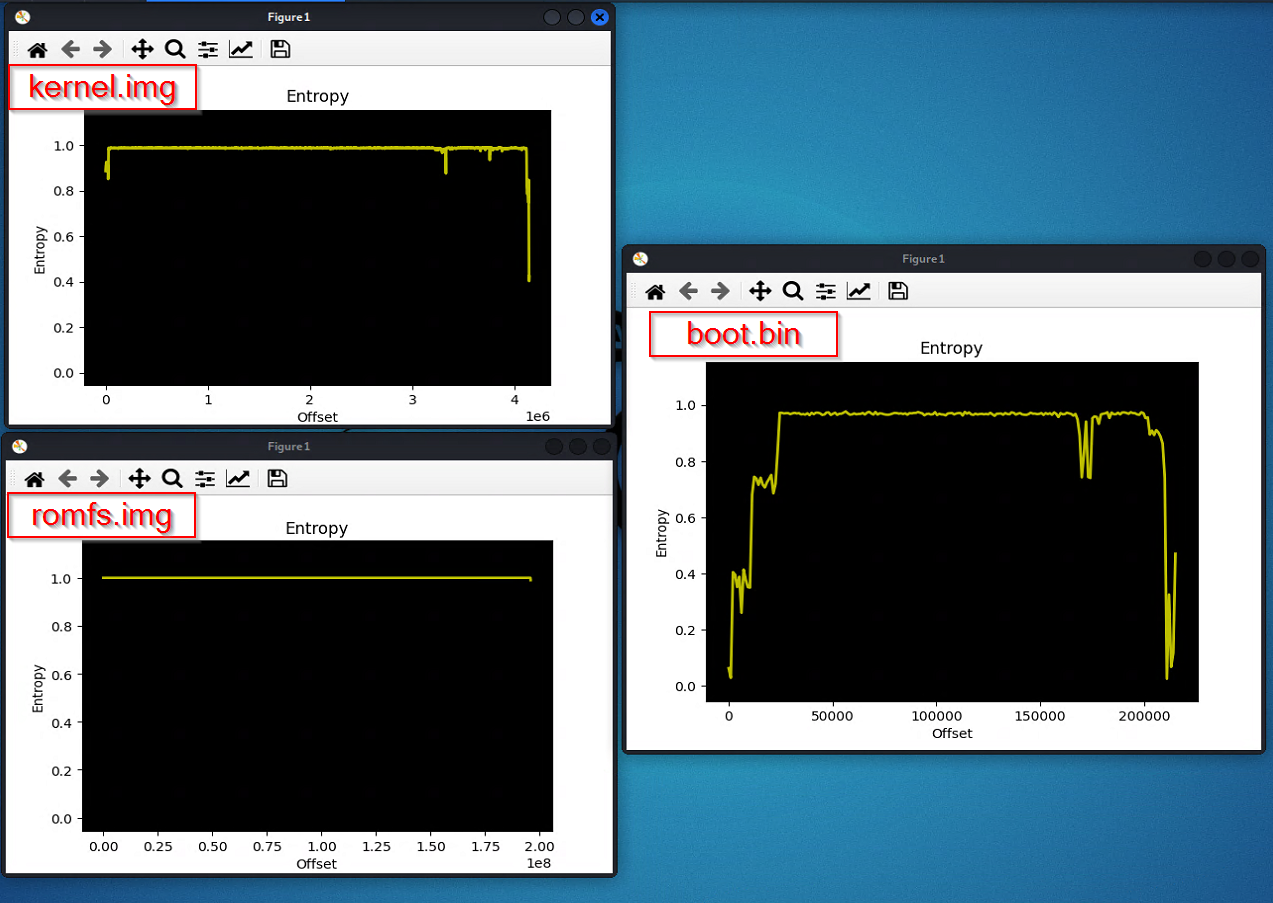
--entropyflag, to check the entropy of all the firmware files. As you can notice from the graph in the picture, most of the files have an almost perfectly flattered Y-axis entropy value of one (1) - this confirms they are encrypted.
The
boot.binfile instead stands out as it doesn’t have a high constant entropy. See those drops? That’s the repetitions we talked about. We can therefore make an educated guess about the fact that the clear-text bootloader is the one in charge of decrypting the other partitions during the boot process, right before starting kernel execution.
https://www.shielder.com/blog/2022/03/reversing-embedded-device-bootloader-u-boot-p.1/