During the compilation of the executable, consistent section names are added by the compilers. The following table outlines some of the common sections in a PE file:
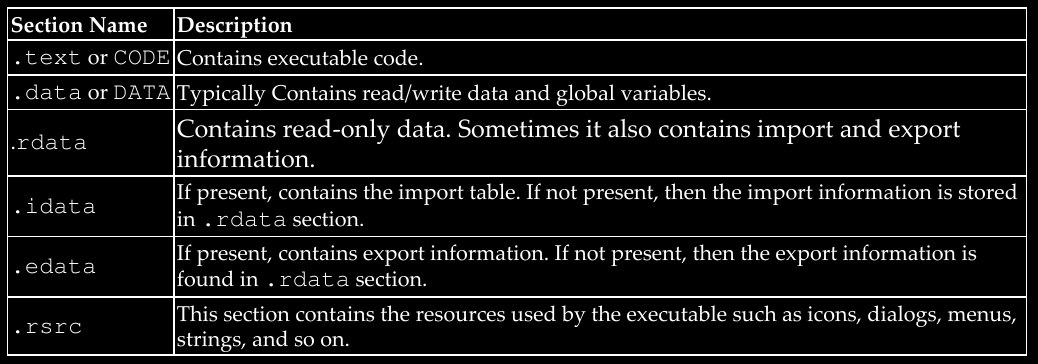
These section names are mainly for humans and are not used by the operating system, which means it is possible for an attacker or an obfuscation software to create sections with different names. If you come across section names that are not common, then you should treat them with suspicion, and further analysis is required to confirm maliciousness.
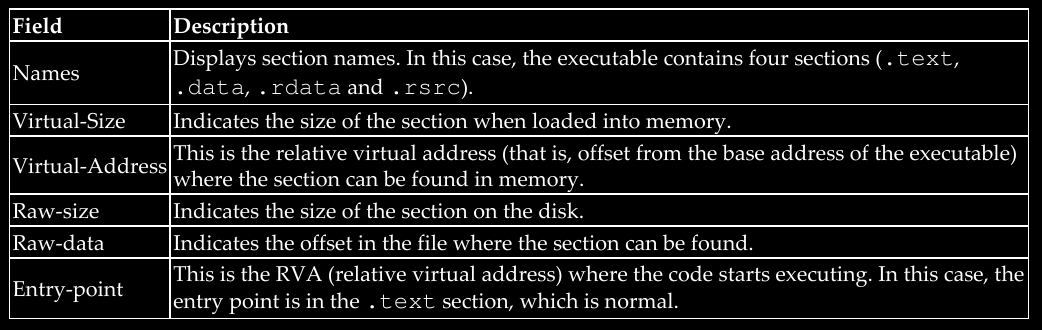
Information about these sections (such as section name, where to find the section, and its characteristics) is present in the section table in the PE header. Examining a section table will give information about the section and its characteristics.
When you load an executable in pestudio and click on sections, it displays the section information extracted from the section table and its attributes (read/write and so on). The next screenshot from pestudio shows the section information for an executable, and some relevant fields from the screenshot are explained here:
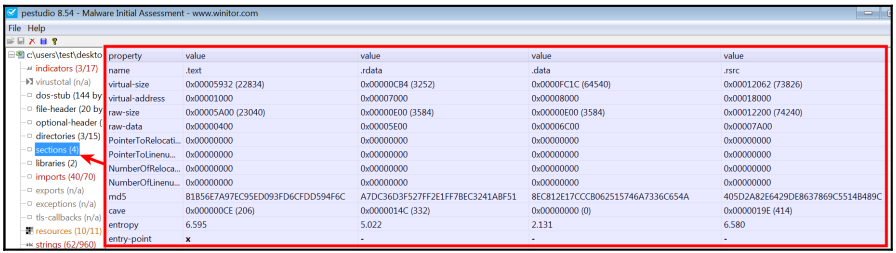
Examining the section table can also help in identifying any anomaly in the PE file. The following screenshot shows the section names of a malware packed with UPX; the malware sample contains the following discrepancies:
- The section names do not contain common sections added by the compiler (such as .text, .data, and so on) but contain section names UPX0 and UPX1.
- The entry point is in the UPX1 section, indicating that execution will start in this section (decompression routine).
- Typically, raw-size and the virtual-size should be almost equal, but small differences are normal due to section alignment. In this case, raw-size is 0, indicating that this section will not take up space on the disk, but virtual-size specifies that, in memory, it takes up more space (around 127 kb). This is a strong indication of a packed binary. The reason for this discrepancy is that when a packed binary is executed, the decompression routine of the packer will copy decompressed data or instructions into the memory during runtime.