Both traps from sensitive operations in VMs and hypercalls from the host kernel enter HYP mode through an exception on the CPU.
https://developer.arm.com/documentation/102142/0100/Trapping-and-emulation-of-instructions
VMI issues:
https://www.slideshare.net/tklengyel/pitfalls-of-virtual-machine-introspection-on-modern-hardware
![[Untitled 123.png|https://ziyang.eecs.umich.edu/esds/papers/hwang-xen.pdf]]
Applied Cryptography and Network Security: 18th International Conference, ACNS 2020, Rome, Italy, October 19–22, 2020, Proceedings, Part II
https://link.springer.com/chapter/10.1007/978-3-030-57878-7_17
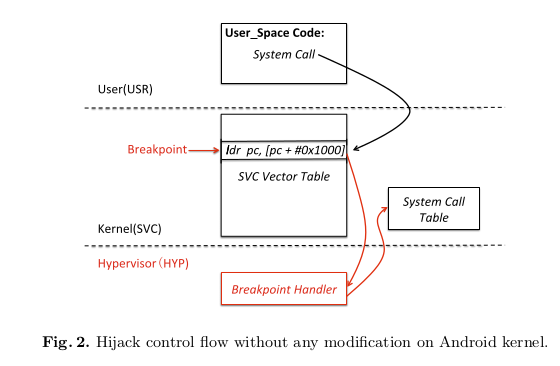
Intercept System Call: On ARMv7,** Breakpoint Control Register (DBGBCR) and Break Value Register (DBGBVR)** control the hardware breakpoints. Putting Super Root: A New Stealthy Rooting Technique on ARM Devices the virtual address of the target instruction into DBGBVR and setting DBG- BCR.E to 1 will enable a breakpoint. When CPU fetches the instruction tagged with the breakpoint, an exception will be generated and handled by the break- point handler. However, in the virtualization environment, when the Trap Debug exceptions (TDE) bit in HYP Debug Configuration Register (HDCR) is set to 1, this exception will be routed to HYP mode. On ARMv7, system call entry is at the Kernel Exception Vectors (SVC Vector Table) with the offset 0x8. If the vector bit in System Control Register (SCTLR.V) is 1, the base address of SVC vectors is at the virtual address 0xFFFF0000. When SCTLR.V is 0, Vector Base Address Register (VBAR) holds the SVC Vectors base address. Reading the values of SCTLR and VBAR registers in hypervisor space, the attacker can locate the system call entry and set the breakpoint on it to intercept all the system calls (Fig. 2). The debug configuration registers DBGBCR, and DBGBVR can be accessed from SVC mode. To prevent Android kernel from modifying DBGBVR and DBGBCR registers, the attacker can set HDCR.{TDRA, TDOSA, TDA} to 1 to trap debug OS-related register access.
https://link.springer.com/chapter/10.1007/978-3-319-69471-9_15
The main challenge in the interception module is the way of intercepting the system call. Although setting HCR.TGE to 0x1 can route all the system call to the hypervisor, the hypervisor needs to simulate all the system calls which makes the hypervisor more complex. Therefore, a piece of hook code is added to enter the hyp mode actively. Original System Call Flow. After the swi instruction is issued, the Program Counter (PC) jumps to the exception vector table in the supervisor mode. The offset of the supervisor call is 0x8, running “ldr pc, vectors start+0x1000”. This instruction then loads the value saved in the address vectors start+0x1000 into PC. And the value is the start address of the system call handler. Hook. At the system boot time, the hypervisor creates a new page to place the hook code and sets the page inaccessible. Then it saves the original value at the address vectors start+0x1000 and replaces it with the start address of the hook code. The hook code issues an hvc instruction to get into the hypervisor. After the hypervisor returns, PC will be loaded with the original value at the address vectors start+0x1000. Then the program handles the system call as usual.
Parameter Acquisition
After the program is trapped into the hyp mode, the hypervisor needs to analyze the system call number and the relevant parameters.HypTracker: A Hypervisor to Detect Malwares Through System 203 There are two kinds of instruction sets in ARM, which are ARM and Thumb. 1 Thumb instruction set is a subset of ARM instruction set. Thumb instructions can be shorter than ARM instructions, which can save the memory of the system. In ARM, the T bit of the Current Program Status Register (CPSR) shows whether the current instruction set is Thumb. Namely, 1 means Thumb and 0 represents ARM. Figure 2 shows the format of CPSR. Fig. 2. The format of CPSR Thumb uses Register 7 (R7) to save the system call number. While there are two ways to save the system call number in ARM instruction set. Two kinds of Application Binary Interface (ABI) are used in ARM: Old Application Binary Interface (OABI) and Embedded Application Binary Interface (EABI). In OABI, the system call number is a parameter of the SVC instruction. While the system call number is saved in R7 in EABI. The parameters in ARM are passed using registers. Register 0 (R0) to Reg- ister 4 (R4) save the needed parameters. The hypervsior will get different kinds of parameters according to the system call number.
SPIDER [10] evaluated the use of injecting software break- points to enable stealthy debugging of processes within virtual machines using the KVM hypervisor. SPIDER achieved signif- icantly better performance than systems relying on two-stage paging for execution tracing, mainly as a result of reducing the scope of trapping.
Similar to SPIDER, SPROBES [11] identified the Secure Monitor Call (SMC) instruction as one possible trapping mechanism for ARM. Unlike the exception caused by the INT3 instruction on x86, SMC is limited to trapping code-execution in supervisor mode (that is, the execution of the guest kernel). Despite such a limitation, it has been proposed as a sufficient method for real-time kernel protection from the ARM TrustZone by researchers at Samsung
Hypervision Across Worlds: Real-time Kernel Protection from the ARM TrustZone Secure World
https://sci-hub.hkvisa.net/10.1145/2660267.2660350
(…) while Intel as well as the AArch64 execution state of ARMv8 CPUs allow to hide memory-artifacts by marking memory pages as execute-only, second level translation tables of both the AArch32 execution state of ARMv8 and the ARMv7 architecture prohibit execute-only memory and thus impede stealthy VMI