https://jmpesp.me/malware-analysis-syscalls-example/
https://github.com/jthuraisamy/SysWhispers2
The system service dispatch table is used to look up the function required to handle a given system call. This facility is implemented in the operating system, not by the CPU. On windows:
— — — — — -Userland — — — — — — | — — — Kernel Land — — —
RPM —> NtReadVirtualMemory —> SYSCALL —> NtReadVirtualMemory
Kernel32 — — ntdll — — — — — — — — — — — — — — — — ntoskrnlThere are two ways a program can make a system call: by using interrupt 0x2E, or by using the SYSENTER instruction.
On Windows XP and beyond, programs typically use the SYSENTER instruction, while older platforms use interrupt 0x2E. The two mechanisms are completely different, although they achieve the same result. Making a system call results in the function KiSystemService being called in the kernel. This function reads the system-call number from the EAX register, and looks up the call in the SSDT. KiSystemService also copies the arguments for the system call from the user-mode stack onto the kernel-mode stack. The arguments are pointed to by the EDX register.
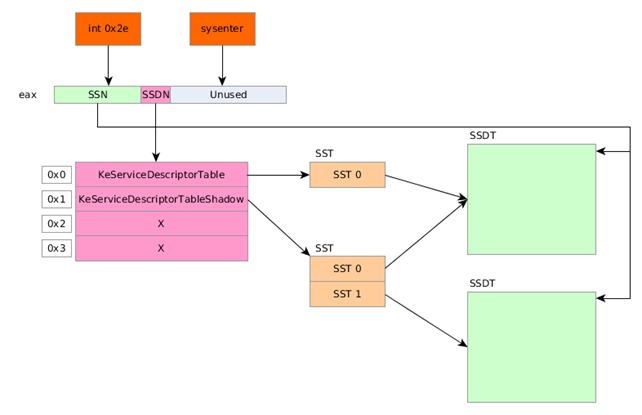
The Service Descriptor Table Number (SDTN) points to one of the 4 SDT tables, where only the first two are actually used and point to the SST. The KeServiceDescriptorTable points to one SST, which further points to the SSDT table. The KeServiceDescriptorTableShadow points to two SSTs where the first one points to the same SSDT table and the second one point to a secondary SSDT table.