- Thumb mode → jump addresses have to be odd
As an example we will reverse engineer the Trafman challenge from rwthCTF. See that IDA failed to disassemble the first instructions:
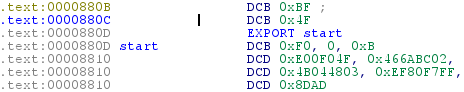
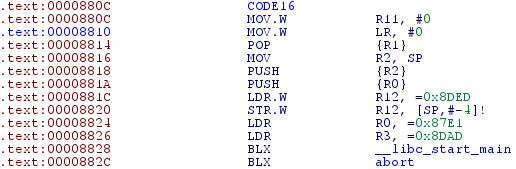
This is because start is located at the uneven address 0x880D. In other words the binary starts executing in Thumb mode at address 0x880C, but IDA thinks it starts executing at 0x880D. We fix this by selecting address 0x880C, pressing ALT+G, and changing the value to 1 (this tells IDA that Thumb code is located at this address). Now again select address 0x880C and press C to directly convert the section to code.
https://www.mathyvanhoef.com/2013/12/reversing-and-exploiting-arm-binaries.html