https://docs.microsoft.com/en-us/sysinternals/downloads/vmmap
Example:
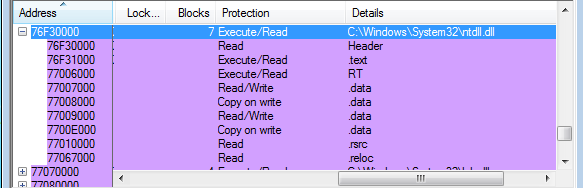
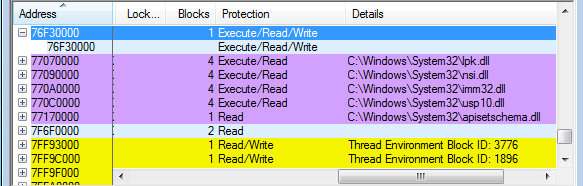
Malware replaced the existing ntdll image on explorer.exe with a newly created section containing an inline hook on NtClose() and code responsible for starting svchost.exe. Output of VMmap indicates that an image of ntdll no longer exists and replaced with a shared Executable/Readable/Writable section after this injection.
https://standa-note.blogspot.com/2015/03/