Cryptography is the art of transforming information security problems into key management problems - Former coworker
Modern Cryptanalysis: Techniques for Advanced Code Breaking - Christopher Swenson
https://swenson.io/Modern%20Cryptanalysis%20v1.1%202022-01-23.pdf
Real-World Cryptography
https://www.amazon.com.br/Real-World-Cryptography-David-Wong/dp/1617296716
https://leanpub.com/gocrypto/read
https://wiki.nikiv.dev/security/cryptography/
RULES TO FOLLOW
Rule 1: Do not use ECB mode for encryption.
Rule 2: Do not use a non-random IV for CBC encryption.
Rule 3: Do not use constant encryption keys.
Rule 4: Do not use constant salts for PBE.
Rule 5: Do not use fewer than 1,000 iterations for PBE.
Rule 6: Do not use static seeds to seed SecureRandom()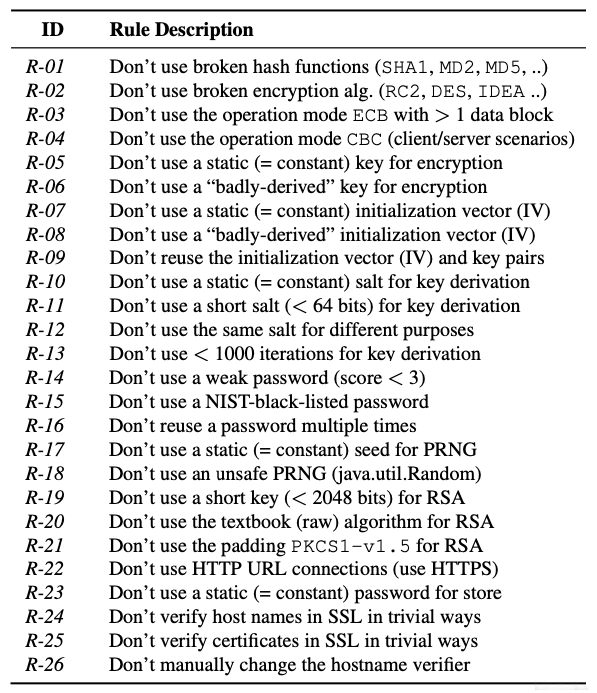
https://gchq.github.io/CyberChef/