Public-Key
Public-key cryptography is based on the concept of a key pair, which consists of a public key and a private key. Data that has been encrypted with a public key can be decrypted only with the corresponding private key. Conversely, data that has been encrypted with a private key can be decrypted only with the corresponding public key.
https://docs.oracle.com/cd/E19509-01/820-3503/ggbgc/index.html
Public-key cryptosystems are based on the concept of trapdoor functions. A one-way function is a function that is easy to compute, but whose inverse is hard to compute. A trapdoor function is like a one-way function, but there is a “magic” value that makes the inverse easy to compute.
If you have a trapdoor function, you can use it to make a public-key encryption algorithm: going forward (in the easy direction), the function encrypts; going backward (in the hard direction), the function decrypts. The magic value required to decrypt is the private key.
If you have a trapdoor function, you can also use it to make a digital signature algorithm: going backward (in the hard direction), the function signs; going forward (in the easy direction), the function verifies a signature. Once again, the magic value required to sign is the private key.
Can you encrypt with a private key and decrypt with a public key?
Yes! In fact, this is exactly how digital signatures work.
Can you find the private key from the public key?
In most asymmetrical crypto system implementation, like RSA, the only fact that is ensured is that you cannot find the private key from the public key. The other way round, finding the public key from the private key is trivial in most case.
For instance, in RSA, you can create public key from private key with:
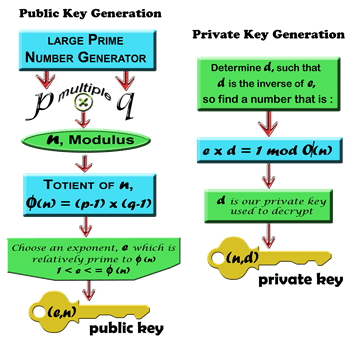
openssl rsa -in private.pem -pubout -out public.pemHow the keys are created?
https://www.youtube.com/watch?v=4zahvcJ9glg
https://www.youtube.com/watch?v=-LyDHLoqNRE
https://www.youtube.com/watch?v=JD72Ry60eP4