WINDOWS:
Translation lookaside buffer (TLB)
https://minnie.tuhs.org/CompArch/Lectures/week06.html
Address translation:
Usual Translation:
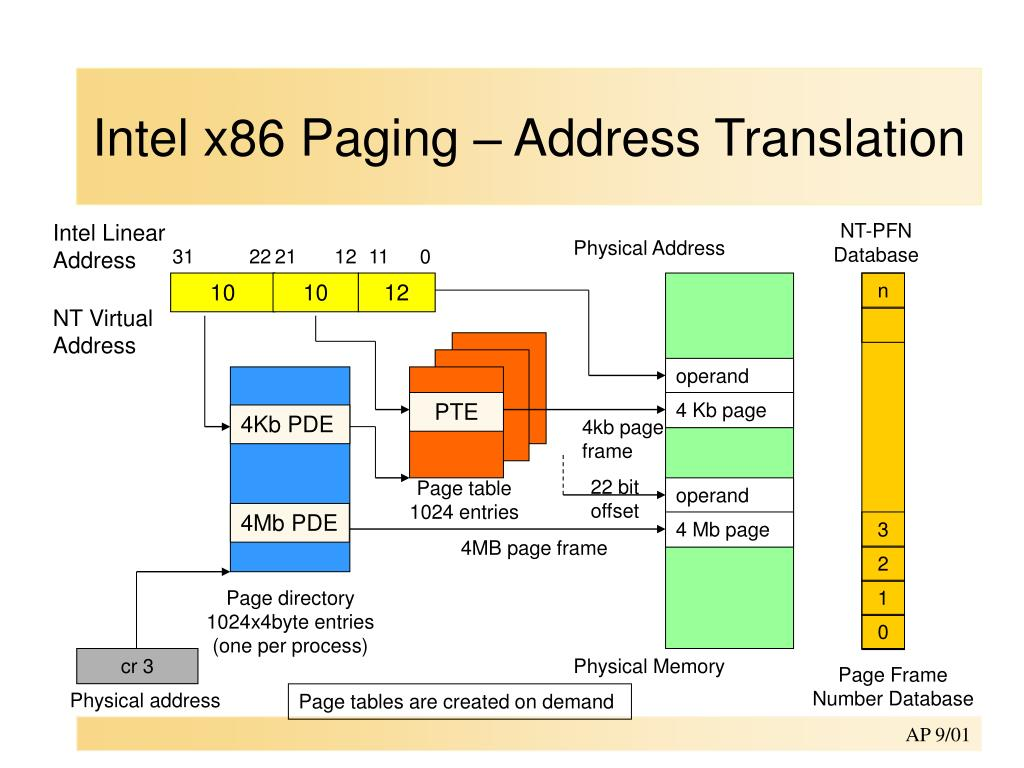
Logical address --> GDT --> Linear address --> Page tables --> Physical Address
(segment:offset) (segment base + offset)
\______________________________________________________/
Virtual address
(can be either logical or linear)If running in VMX non-root mode (i.e. in a VM) and EPT is enabled then:
Logical address --> GDT --> Linear address --> Page tables --> Guest Physical Address --> EPT --> (System) Physical Address
(segment:offset) (segment base + offset)
\______________________________________________________/ \__________________________________________________________/
Virtual address Physical address
(can be either logical or linear)If an IOMMU is present (like the umbrella technology VT-d, dma and etc):
Logical address --> GDT --> Linear address --> Page tables --> Guest Physical Address --> EPT --> (System) Physical Address --> 1 or 2 level translation --> (IO) Physical address
(segment:offset) (segment base + offset)
\______________________________________________________/ \___________________________________________________________________________________________________________________/
Virtual address Physical address
(can be either logical or linear)X64 EXAMPLE:
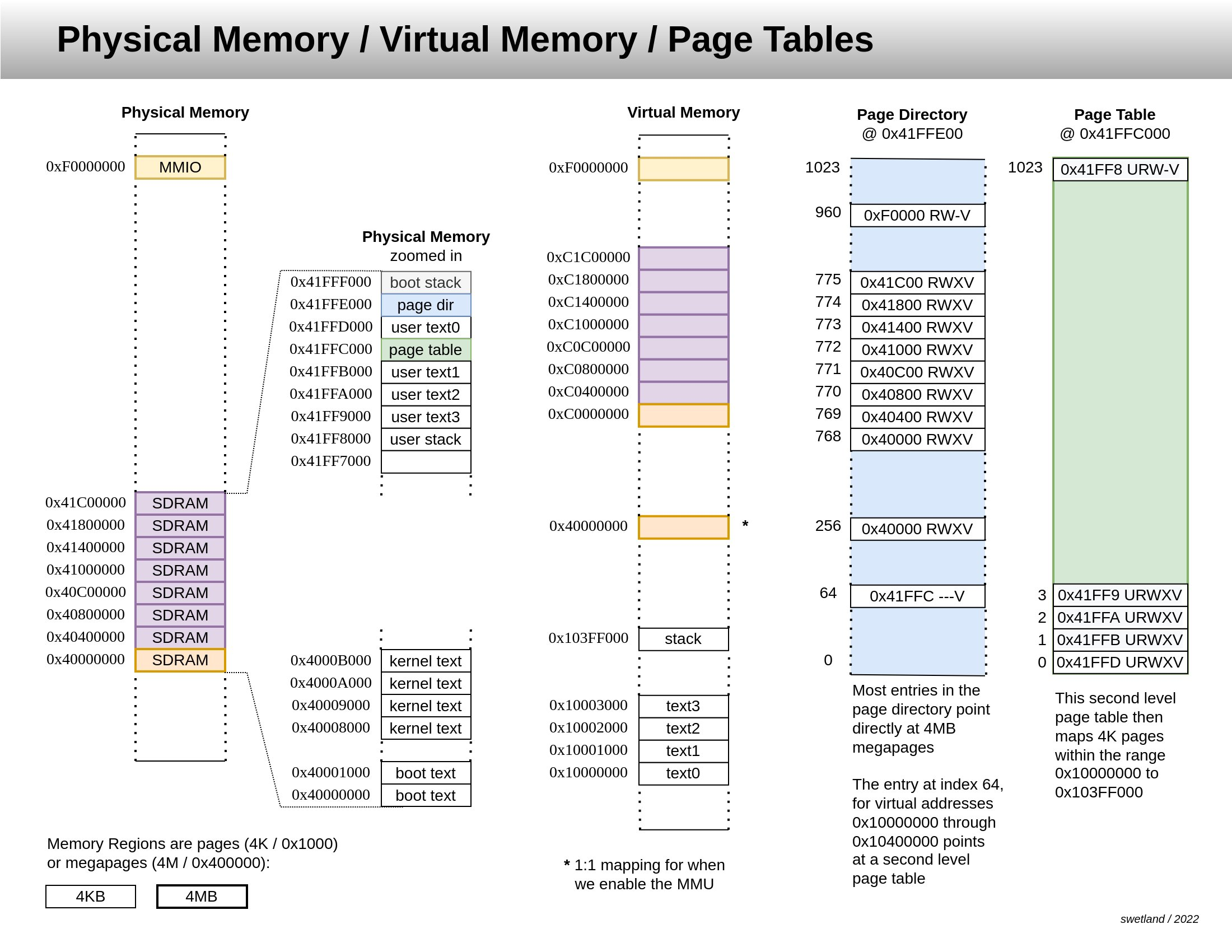
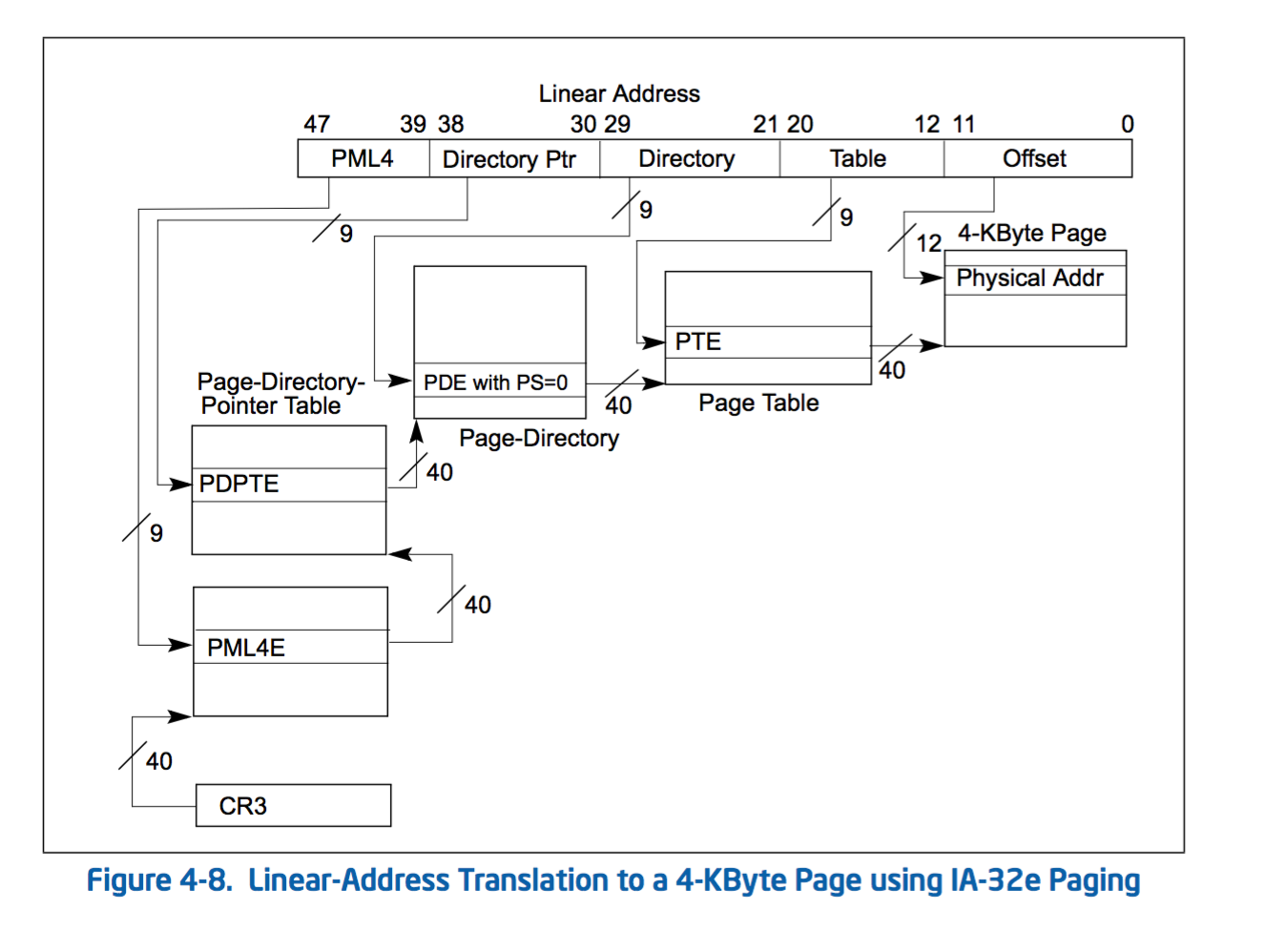
X64 paging uses 4 levels of tables to map a physical page to a virtual page. They are PML4 (aka PXE), PDPT, PD and PT. Control Register CR3 contains the (physical) base address of the PML4 table for the current process.
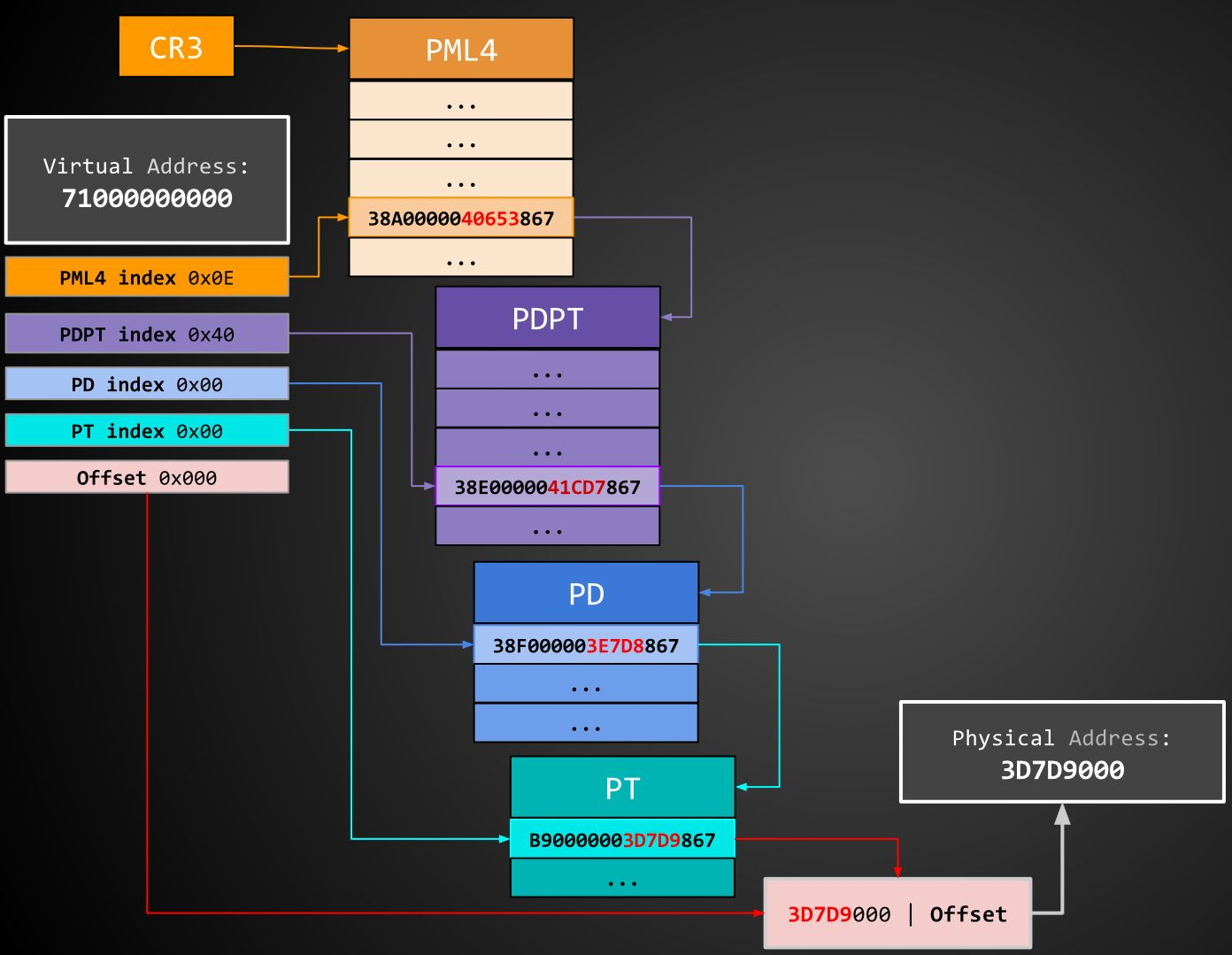
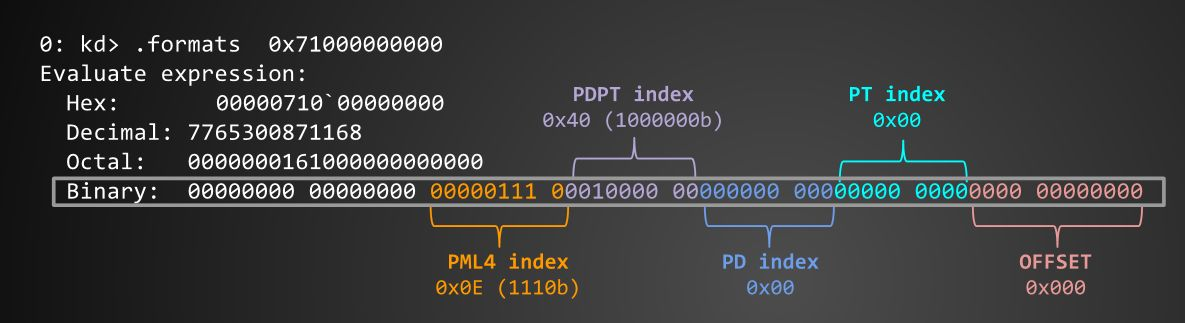
If we would like to walk the paging tables of (for example) virtual address 0x71000000000:
First, we decompose it:
https://www.cs.uic.edu/~jbell/CourseNotes/OperatingSystems/9_VirtualMemory.html
https://courses.engr.illinois.edu/cs241/sp2014/lecture/09-VirtualMemory_II_sol.pdf