“The VM-execution control fields govern VMX non-root operation.”
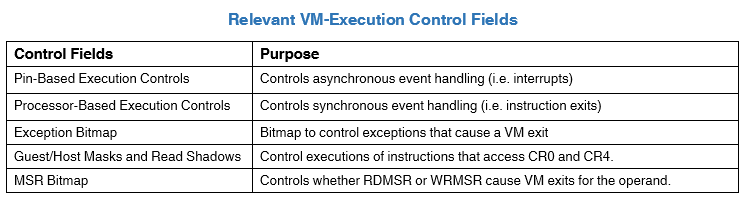
- The first control field in the table is the
Pin-Based Execution Control. It is a 32-bit vector that controls the handling of asynchronous events in the guest.- If the guest encounters a non-maskable interrupt we could set a control bit that will cause a
VM exitany time an attempt to deliver anNMIis made. This structure will be zeroed for our project, however, it will be important in a later series on APIC virtualization.
- If the guest encounters a non-maskable interrupt we could set a control bit that will cause a
union __vmx_pinbased_control_msr_t
{
unsigned __int64 control;
struct
{
unsigned __int64 external_interrupt_exiting : 1;
unsigned __int64 reserved_0 : 2;
unsigned __int64 nmi_exiting : 1;
unsigned __int64 reserved_1 : 1;
unsigned __int64 virtual_nmis : 1;
unsigned __int64 vmx_preemption_timer : 1;
unsigned __int64 process_posted_interrupts : 1;
} bits;
};- The next control field in the table is great for control of the hypervisor when it get to the launch phase. There are actually two 32-bit vectors that control the handling of synchronous events referred to as the
primary processor-based VM-execution controlsand thesecondary processor-based VM-execution controls.- These two vectors control events that occur by the execution of specific instructions such as cpuid, or rdmsr, or rdtsc to name a few.
union __vmx_primary_processor_based_control_t
{
unsigned __int64 control;
struct
{
unsigned __int64 reserved_0 : 2;
unsigned __int64 interrupt_window_exiting : 1;
unsigned __int64 use_tsc_offsetting : 1;
unsigned __int64 reserved_1 : 3;
unsigned __int64 hlt_exiting : 1;
unsigned __int64 reserved_2 : 1;
unsigned __int64 invldpg_exiting : 1;
unsigned __int64 mwait_exiting : 1;
unsigned __int64 rdpmc_exiting : 1;
unsigned __int64 rdtsc_exiting : 1;
unsigned __int64 reserved_3 : 2;
unsigned __int64 cr3_load_exiting : 1;
unsigned __int64 cr3_store_exiting : 1;
unsigned __int64 reserved_4 : 2;
unsigned __int64 cr8_load_exiting : 1;
unsigned __int64 cr8_store_exiting : 1;
unsigned __int64 use_tpr_shadow : 1;
unsigned __int64 nmi_window_exiting : 1;
unsigned __int64 mov_dr_exiting : 1;
unsigned __int64 unconditional_io_exiting : 1;
unsigned __int64 use_io_bitmaps : 1;
unsigned __int64 reserved_5 : 1;
unsigned __int64 monitor_trap_flag : 1;
unsigned __int64 use_msr_bitmaps : 1;
unsigned __int64 monitor_exiting : 1;
unsigned __int64 pause_exiting : 1;
unsigned __int64 active_secondary_controls : 1;
} bits;
};union __vmx_secondary_processor_based_control_t
{
unsigned __int64 control;
struct
{
unsigned __int64 virtualize_apic_accesses : 1;
unsigned __int64 enable_ept : 1;
unsigned __int64 descriptor_table_exiting : 1;
unsigned __int64 enable_rdtscp : 1;
unsigned __int64 virtualize_x2apic : 1;
unsigned __int64 enable_vpid : 1;
unsigned __int64 wbinvd_exiting : 1;
unsigned __int64 unrestricted_guest : 1;
unsigned __int64 apic_register_virtualization : 1;
unsigned __int64 virtual_interrupt_delivery : 1;
unsigned __int64 pause_loop_exiting : 1;
unsigned __int64 rdrand_exiting : 1;
unsigned __int64 enable_invpcid : 1;
unsigned __int64 enable_vmfunc : 1;
unsigned __int64 vmcs_shadowing : 1;
unsigned __int64 enable_encls_exiting : 1;
unsigned __int64 rdseed_exiting : 1;
unsigned __int64 enable_pml : 1;
unsigned __int64 use_virtualization_exception : 1;
unsigned __int64 conceal_vmx_from_pt : 1;
unsigned __int64 enable_xsave_xrstor : 1;
unsigned __int64 reserved_0 : 1;
unsigned __int64 mode_based_execute_control_ept : 1;
unsigned __int64 reserved_1 : 2;
unsigned __int64 use_tsc_scaling : 1;
} bits;
};-
The third control field is the
exception bitmap, this control field is a 32-bit field that contains a bit for an exception. When an exception occurs in the guest, it’s control field is used to determine if the exception should cause a VM exit or be delivered normally through theIDTusing the descriptor that matches the exception’s vector. -
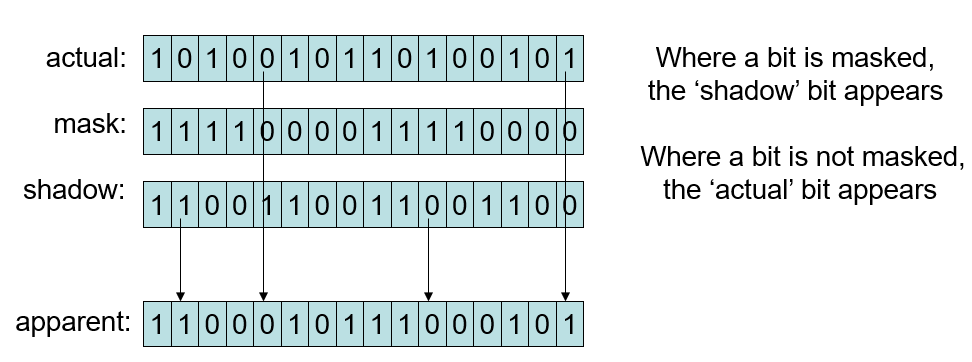
The fourth control field in the table is the
Guest/Host Mask and Read ShadowsforCR0, andCR4. These fields control execution of instructions that access those registers.- In general, special VMCS control-components allow your VMM to modify values read from
CR0andCR4. If the bits in the guest/host mask are set to 1 then they are owned by the host which means if the guest attempts to set them to values different from the bits in the read shadow for the respective control register then a VM exit will occur. Any guest that reads the values for these bits through use of typical instructions will read values from the read shadow for the respective control register. If bits are cleared to 0 in the guest/host mask then they are owned by the guest, meaning that any attempt by the guest to modify or read them succeeds and returns the bits from the respective control register.
- In general, special VMCS control-components allow your VMM to modify values read from
2. The last control field part of the VM-execution control fields is the `MSR bitmap`.
1. This bitmap controls whether the execution of rdmsr or wrmsr causes a VM exit. It only causes a VM exit if the value in `RCX` is not in the range of MSR’s supported by the bitmap, or the bit in the MSR bitmap that corresponds to the value of `RCX` is 1.
2. The `MSR bitmap` is comprised of 4 contiguous memory blocks – each 1-KByte in size. You can allocate this entire bitmap in one go using `MmAllocateContiguousMemory` and specifying the size to be 4-KByte’s or using the `PAGE_SIZE` macro.