https://redops.at/en/blog/direct-syscalls-vs-indirect-syscalls
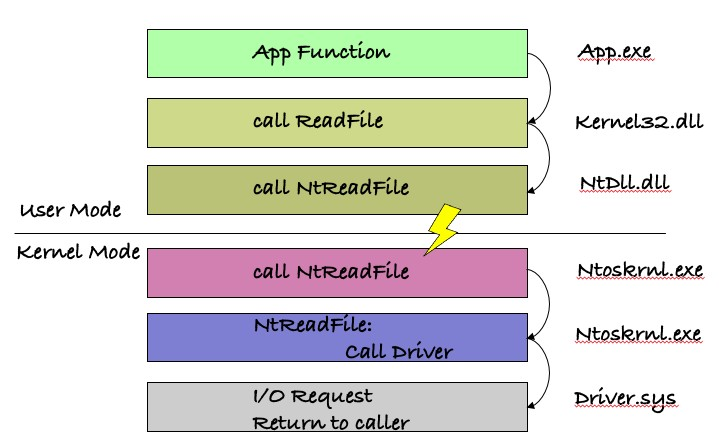
As an example of how the OS layers are built on top of each other, let’s take a look at a kernel32.dll API function such as ReadFile.
When ReadFile is invoked, the implementation that resides in kernel32.dll will parse the parameters passed to it and will call the undocumented NtReadFile in ntdll.dll.
Later, NtReadFile will set eax with the appropriate syscall number and will execute the SYSENTER instruction (or SYSCALL instruction in x64).
The SYSENTER instruction will create a trap and switch to kernel mode by calling the address that is stored in the MSR 0x176 (in x86 or LSTAR MSR in x64) that points to KiFastCallEntry (KiSystemCall64 in x64).
This function will save the current user-mode context and will set up the kernel context before finally calling the appropriate kernel version of NtReadFile (also can be referred as ZwReadFile). It’s located in ntoskrnl.exe, which will do most of the work and will call the appropriate disk driver to do the actual reading from the disk.