VMI - Virtual Machine Introspection
ARM Hypervisor Security Applications
THEORY
STUDY CASES:
-
RASPVISOR OVERVIEW [[Computer h1t/Virtualization/Arm VE/Running a Binary]]
-
XEN ARM PROJECT
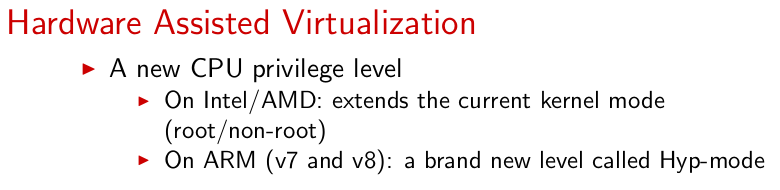
The ARM virtualization extensions are based on the security extensions, commonly known as TrustZone.
https://genode.org/documentation/articles/arm_virtualization#Overall_Architecture
![[Untitled 134.png|https://jyx.jyu.fi/handle/123456789/77233]]
MEMORY
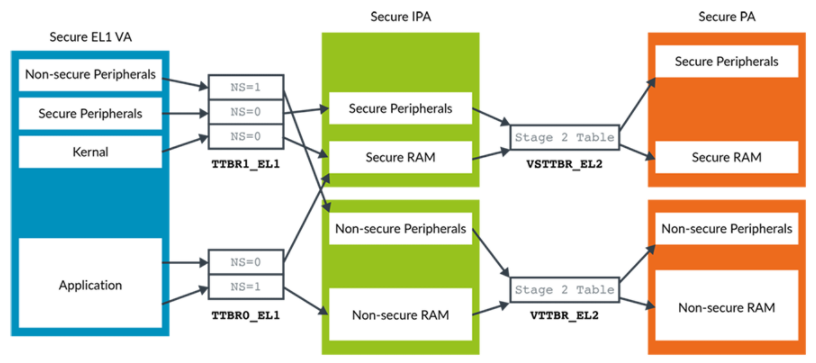
ARM’s virtualization support extends the former MMU by an optional second stage of address translations, thereby effectively realizing nested paging. Moreover, to enable the usage of virtual memory within the hypervisor mode, ARM additionally introduced an exclusive MMU for this mode.
To overcome the limitations of a 32-bit addressable physical memory space, ARM offers a new page table format, which extends the addressable physical memory space to 40 bits. This so called “large physical address extension” (LPAE) is obligatory when using virtualization.
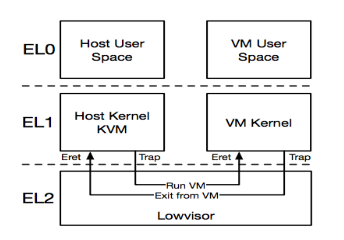
The Arm architecture defines two physical address spaces: Secure and Non-secure. In Non-secure state, the output of the stage 1 translation of a virtual machine (VM) is always Non-secure. Therefore, there is a single Intermediate Physical Address (IPA) space for stage 2 to handle.
![[Untitled 135.png|https://developer.arm.com/documentation/den0024/a/The-Memory-Management-Unit/Translations-at-EL2-and-EL3]]
In Secure state, the stage 1 translation of a VM can output both Secure and Non-secure addresses. The NS bit in the translation table descriptors controls whether the Secure or the Non-secure address space is outputted. As shown in the following diagram, this means that there are two IPA spaces for stage 2, Secure and Non-secure:
https://ashw.io/blog/arm64-pgtable-tool
https://www.genode.org/documentation/articles/arm_virtualization
CONTENT:
https://ashw.io/blog/arm64-hypervisor-tutorial/1?rq=hypervisor
https://wiki.xenproject.org/wiki/Xen_ARM_with_Virtualization_Extensions_whitepaper
https://xenproject.org/2020/09/29/xen-on-raspberry-pi-4-adventures/
https://github.com/dornerworks/xen-rpi4-builder
https://ashw.io/blog/arm64-hypervisor-tutorial/1
https://www.cs.columbia.edu/~nieh/pubs/asplos2014_kvmarm.pdf
https://www.starlab.io/blog/how-the-xen-hypervisor-supports-cpu-virtualization-on-arm
https://www.starlab.io/blog/deep-dive-mmu-virtualization-with-xen-on-arm
https://lwn.net/Articles/557132/
https://blog.impalabs.com/2212_huawei-security-hypervisor.html